
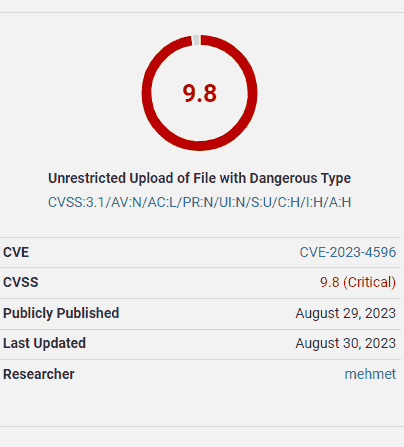
The U.S. Government’s National Vulnerability Database (NVD) has published a notice about a critical vulnerability affecting the Forminator WordPress Contact Form plugin, up to and including version 1.24.6.
Unauthenticated attackers can exploit this vulnerability to upload malicious files to websites, which "may make remote code execution possible."
The vulnerability has a severity rating of 9.8 out of 10, with ten being the most severe level.
Screenshot Of Wordfence Advisory
Screenshot from Wordfence.com
Vulnerability To Unauthenticated Attackers
Many vulnerabilities require an attacker to have a user level within WordPress before they can launch an attack. For example, some vulnerabilities are exploitable by those with a subscriber user level, while others require contributor or admin levels.
What makes this vulnerability particularly concerning is that it allows unauthenticated attackers, those with no user level at all, to successfully hack the site. Another reason why this vulnerability is rated 9.8 is due to the attacker’s ability to upload an arbitrary file, such as a malicious script.
The National Vulnerability Database (NVD) describes the vulnerability:
“The Forminator plugin for WordPress is vulnerable to arbitrary file uploads due to file type validation occurring after a file has been uploaded to the server in the upload_post_image() function in versions up to, and including, 1.24.6.
This makes it possible for unauthenticated attackers to upload arbitrary files on the affected site’s server which may make remote code execution possible.”
Remote Code Execution
A Remote Code Execution (RCE) vulnerability is a type of exploit that allows an attacker to execute malicious code on the attacked website remotely. The damage from such an exploit can be as severe as a complete site takeover.
Contact Forms Must Be Locked Down
WordPress plugins that allow registered or unauthenticated users to upload content, even text or images, must have mechanisms to limit what can be uploaded. Contact forms, in particular, must be locked down since they accept input from the public.
RCE Not Specific To WordPress
These kinds of vulnerabilities are not exclusive to WordPress and can happen to any Content Management System. WordPress has published coding standards to help developers prevent these issues. The WordPress developer page for plugin security (Sanitizing Data) explains how to handle uploads from untrusted sources.
The developer page advises:
“Untrusted data comes from many sources (users, third-party sites, even your own database!) and all of it needs to be checked before it’s used.
Sanitizing input is the process of securing/cleaning/filtering input data.
Validation is preferred over sanitization because validation is more specific.
But when “more specific” isn’t possible, sanitization is the next best thing.”
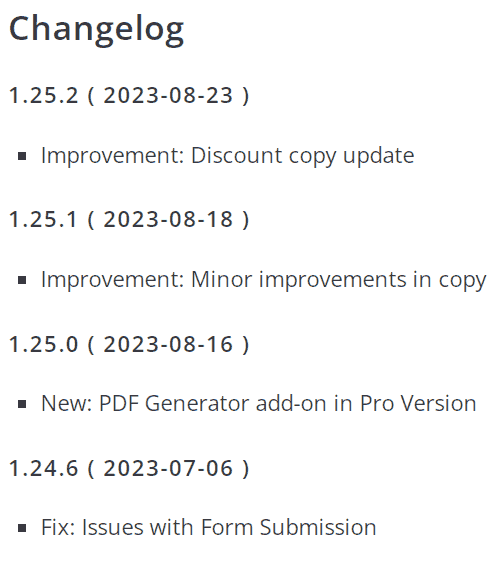
Has the Forminator Contact Form Plugin Fixed The Vulnerability?
According to the National Vulnerability Database and Wordfence, the issue has been addressed in version 1.25.0.
Wordfence recommends updating to the latest version:
“Update to version 1.25.0, or a newer patched version…”
Forminator Plugin Changelog
A changelog is a record of all changes made to software, allowing users to determine whether they want to update their software. It’s important to inform users about fixes for vulnerabilities so they can make an informed decision about updates.
Judge for yourself whether the Forminator changelog offers sufficient notification to their users about a vulnerability patch:
Screenshot of Forminator Changelog
Sources:
- Read the official National Vulnerability Database advisory:
- CVE-2023-4596 Detail
- Read the Wordfence advisory on the Forminator WordPress Contact Form Plugin Vulnerability
- Forminator <= 1.24.6 – Unauthenticated Arbitrary File Upload
- Read the Exploit Database report on the Forminator Contact Form vulnerability
- WordPress Plugin Forminator 1.24.6 – Unauthenticated Remote Command Execution
Featured image by Shutterstock/ViDI Studio



